A website loading again does not always mean the DDoS attack is over.
That is the part many people miss. The biggest traffic flood may have eased, the homepage may be back, and some users may be getting through again. But behind the scenes, a service can still be dealing with malicious traffic, lingering instability, packet loss, overloaded systems, or repeat bursts designed to test whether defenses have weakened. That is especially relevant now, as recent reporting from NETSCOUT, Cloudflare, Imperva, and others shows that modern DDoS attacks are not only growing in scale, but also becoming faster, more frequent, and easier to launch.
So when people ask whether a DDoS attack is over, what they usually want to know is something more practical. They want to know whether the service is truly recovering, whether normal users can rely on it again, and whether the worst is actually behind them.
That is a much better question.
At its core, a distributed denial-of-service attack is meant to make a service unavailable or harder to use by overwhelming it with attack traffic, exhausting resources, or disrupting normal access for legitimate users. Depending on the attack type, that can mean crushing the network with raw volume, overloading the application with HTTP or HTTPS requests, or creating enough friction that the service slows to a crawl without going fully offline. Wikipedia’s overview also notes that some attacks are designed as degradation-of-service attacks, meaning the target may still function, just badly enough to frustrate users and damage the business.
That distinction matters because recovery is not always obvious. If a site is still technically reachable but users are timing out at checkout, failing logins, or dealing with unstable pages, the service may not be truly recovered even if it looks “up” on the surface.
This is where many articles on the topic fall short. A service can look stable before it is actually safe.
One reason is that DDoS mitigation often starts working before the full incident is finished. Traffic filtering, rate limiting, scrubbing, CDN support, and other defensive measures can restore partial usability while the attack is still ongoing in the background. That means a site may come back for some users while the infrastructure is still under unusual strain. Cloudflare’s reporting on the evolution of attack size helps explain why this matters. The company shows that DDoS campaigns have grown dramatically across bits per second, packets per second, and requests per second, which means even short bursts can create serious disruption and messy recovery windows.
Another reason is that attackers often do not operate in one clean wave. NETSCOUT’s map and related monitoring tools focus on ongoing global DDoS activity, highlighting that attack conditions can shift fast across time and geography. A service may recover from the first visible flood and then get hit again by smaller or more targeted bursts.
There is also the business side of the problem. Even if the worst traffic has dropped, systems may still be handling error spikes, cache issues, backend stress, or application-level instability. In other words, “back online” is not always the same thing as “back to normal.”
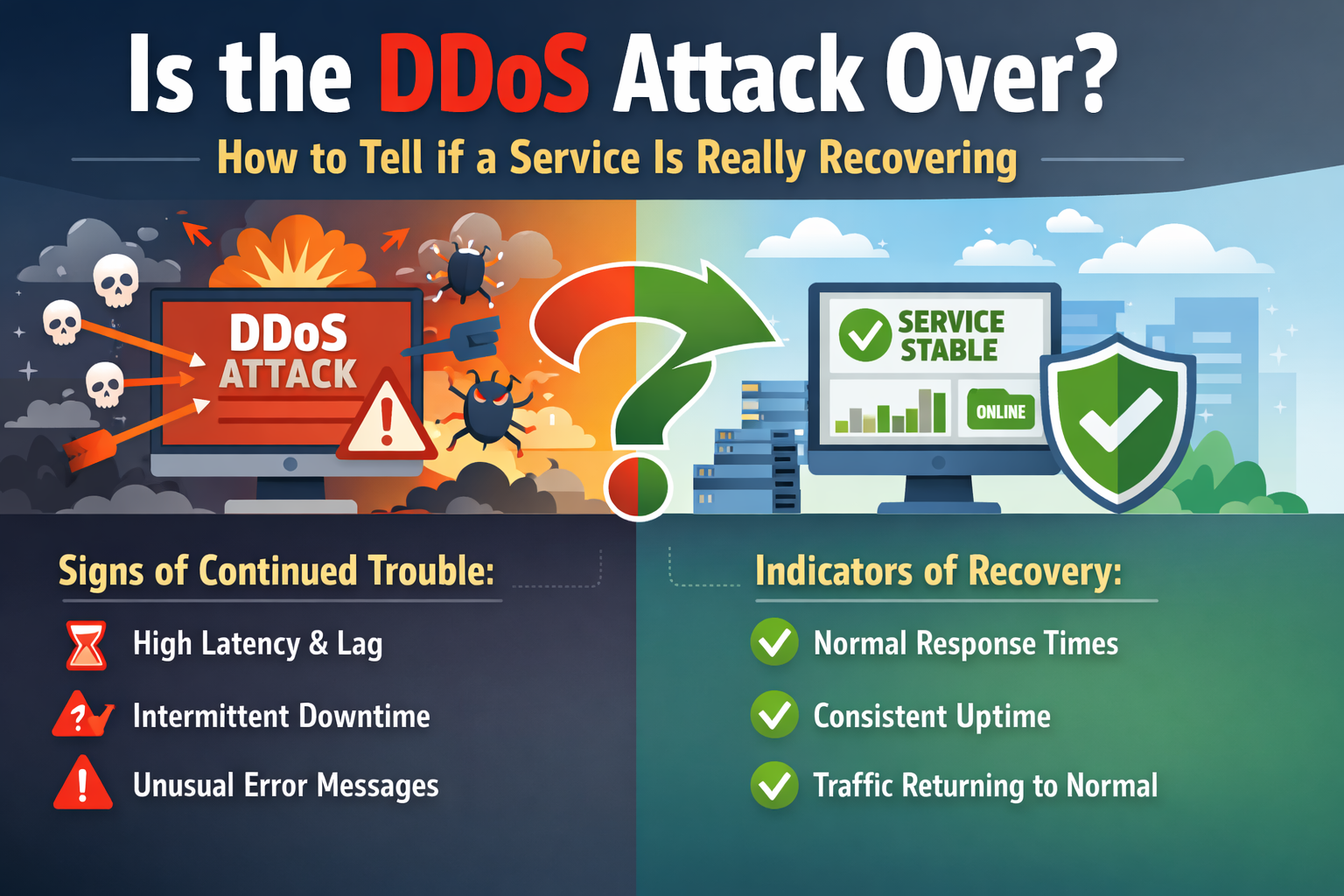
The most reliable way to judge recovery is not by one positive signal. It is by a pattern of normal behavior returning across several areas at once.
One of the clearest signs of real recovery is when traffic volume starts looking normal again instead of showing unusual spikes, erratic patterns, or repeated surges. That includes bandwidth, requests per second, and other load signals. If the service has a known baseline and current traffic is settling back near that level without fresh abnormal bursts, that is a strong sign the attack pressure is easing. This matters because recent industry reporting shows how large modern attacks can get. Imperva described early 2025 DDoS attacks as part of a dangerous trend in cybersecurity, while CSO Online reported that botnet-driven attacks and DDoS-for-hire services continue to expand attack capacity.
A service that is really recovering should show improving response times, lower error rates, and fewer signs of network congestion or resource exhaustion. If users are still seeing random failures, long waits, or connection resets, the incident may not be done. A live system should not just load occasionally. It should behave consistently.
This is one of the best practical tests. Can users sign in? Can they search, upload, pay, or complete core workflows without unusual friction? If the answer is yes across different locations and normal traffic conditions, recovery is much more believable.
This point matters because a DDoS attack does not need to fully knock out the target to be effective. If users cannot complete real tasks, the service is still hurting. Wikipedia’s discussion of partial service degradation supports this broader view of impact.
It is a good sign when DDoS mitigation tools stop absorbing clearly abnormal load. That could mean the WAF, scrubbing service, load balancer, or other defensive layers are no longer being forced into aggressive protective behavior just to keep the service standing. If defenses remain highly active for long periods, the attack may still be present even if users see fewer obvious symptoms.
This is where the real answer often lives.
A common sign that the incident is still active is when traffic calms down and then spikes again. These bursts may be smaller than the original flood, but they can still keep the service unstable or test whether defenses have relaxed. Monitoring-driven pages like NETSCOUT’s DDoS Attack Map and Digital Attack Map reinforce the reality that attack patterns are dynamic rather than fixed.
If users keep reporting sluggish pages, connection drops, or failed actions, the service may still be dealing with residual damage or ongoing low-level pressure. A platform does not need to be fully offline to still be under attack.
Sometimes the network side improves first, but the application or origin systems remain shaky. That can happen when backend services, databases, queues, or session systems have been stressed hard during the incident. In those cases, the traffic flood may be lower, but the customer experience still is not normal.
If incident teams still have temporary emergency controls in place, such as extreme rate limiting, manual traffic blocks, or emergency routing changes, it may be too early to say the service has fully recovered. A stable service should not need crisis settings forever.
One reason this keyword is so interesting is that people assume longer attacks are always the bigger problem. That is not necessarily true.
StationX reports that 89% of DDoS attacks now last under 10 minutes, with an average duration of about 20 minutes. Yet short attacks can still create major business pain, especially when they happen at the wrong time or hit systems with limited resilience.
That means a service may face a strange situation where the worst of the attack traffic is gone, but the recovery work continues. Teams may still need to validate capacity, check logs, restore normal routing, review performance, confirm that legitimate users are no longer blocked, and watch for renewed pressure.
So the better question is not just how long the attack lasted. It is how long it takes the service to return to dependable, normal behavior.
A service is in a much stronger position when several of these are true at the same time:
Traffic baseline looks normal again.
Latency is back within expected range.
Error rates have dropped to normal levels.
Packet loss is no longer elevated.
Legitimate users can complete core actions consistently.
Origin health is stable.
WAF and other mitigation layers are not seeing unusual strain.
There are no recurring surges from suspicious sources.
Support complaints and user-reported issues are falling back to normal patterns.
This is the kind of operational checklist missing from most of the current search results. The SERP gives plenty of information about attack size, botnets, and global DDoS trends, but much less help for the practical recovery question. That is the gap your article can fill.
Recent trend reporting helps explain why this question keeps coming up.
Cloudflare has shown how attack sizes have climbed over the past decade, including major growth in Tbps, pps, and RPS levels.
CSO Online reported on how botnet-driven attacks evolved in the second half of 2025, noting the role of AI, IoT botnets, and increasingly accessible attack tools.
Imperva warned that early 2025 DDoS attacks point to a more dangerous cybersecurity environment, reinforcing the idea that organizations should prepare for high-intensity disruptions rather than assume older defensive habits are enough.
Put all that together, and it becomes easier to see why services may recover in stages instead of in one neat line. Modern attacks are faster, more flexible, and more capable of returning in waves.
The honest answer is this: not just because the site is loading again.
A DDoS attack is more likely to be over when attack traffic has dropped back toward baseline, latency and error rates have normalized, legitimate users can complete their tasks without unusual friction, and mitigation tools are no longer absorbing suspicious spikes in the background. When those conditions hold steadily, the service is not just back online. It is actually recovering.
That is the difference that matters.
A short return to normal can be good news, but real recovery is about stability, not a single moment. The safer mindset is to treat recovery as a pattern you confirm, not a guess you make.