When people compare spear phishing and whaling, they often stop at one simple point: one targets regular employees, the other goes after executives. That is true, but it barely scratches the surface.
The real difference is in how the attack is built, how much research goes into it, what the attacker wants to achieve, and how damaging the result can be. Across the competitor pages you shared, the common thread is clear. Both are highly targeted forms of phishing built on social engineering, but whaling usually aims at the people with the most authority, the biggest access, and the highest financial value.
That matters because a fake message sent to an accounts payable staff member is dangerous, but a convincing request sent to a CEO, CFO, or another C-suite leader can trigger a wire transfer, expose confidential documents, or create a serious business email compromise event in a matter of minutes.
Spear phishing is a targeted cyberattack in which the attacker pretends to be a trusted person or organization and sends a tailored message to a specific person or group. The goal is usually to get the victim to click a link, open an attachment, reveal credentials, install malware, or hand over sensitive business information. Imperva describes it as a social engineering attack that can lead to stolen data, malicious code, or even the first stage of an advanced persistent threat.
What makes spear phishing different from broad, generic phishing is the level of personalization. These messages are not random. Attackers often use details pulled from social media profiles, company websites, public records, internal context, or earlier phishing attempts. That extra context makes the email feel believable. Kent State’s guidance points out that attackers may already know a target’s name, role, employer, hometown, or even other personal details before they ever send the message.
In practice, spear phishing often targets people like HR managers, IT administrators, finance employees, or team members who have access to useful systems and data. A message may look like it came from the IT department, a trusted vendor, or a coworker asking for a quick action. The attacker is usually trying to gain a foothold, steal login details, or move deeper into the organization.
Whaling is commonly described as a form of spear phishing that focuses specifically on high-value targets such as executives, decision-makers, and other senior leaders. Huntress defines it as a phishing attack aimed at high-level leaders like the CEO, CFO, and other C-suite executives in order to steal money or sensitive information.
The reason whaling gets special attention is simple. These people often have authority to approve payments, access strategic files, or influence important operational decisions. That means the attacker does not always need broad access into the company. If they can successfully manipulate one senior person, the payoff can be immediate and massive. Huntress notes that whaling can lead to multi-million-dollar losses, operational disruption, and long-term reputational harm.
Kent State’s security guidance also highlights that whaling messages often appear to come from a real executive and may ask for wire transfers, employee records, payroll files, passwords, or other highly sensitive business information. These attacks are designed to look urgent, legitimate, and routine enough that the target acts before slowing down to verify the request.
At their core, both attacks rely on the same human weaknesses. They use trust, authority, urgency, and deception to push someone into making a bad decision. They also tend to use spoofed email, fake websites, and well-crafted language to look real.
Both can involve:
Impersonation, spoofed domains, malicious links, fake login pages, credential theft, data exfiltration, account compromise, malware delivery, backdoor access, and reputational damage.
Both also start with research. Proton lays out a familiar process: reconnaissance, crafting the bait, delivery, exploitation, and impact. That framework applies to both spear phishing and whaling, although the depth of research is usually much higher in a true whaling attack.
This is where the comparison becomes more useful.
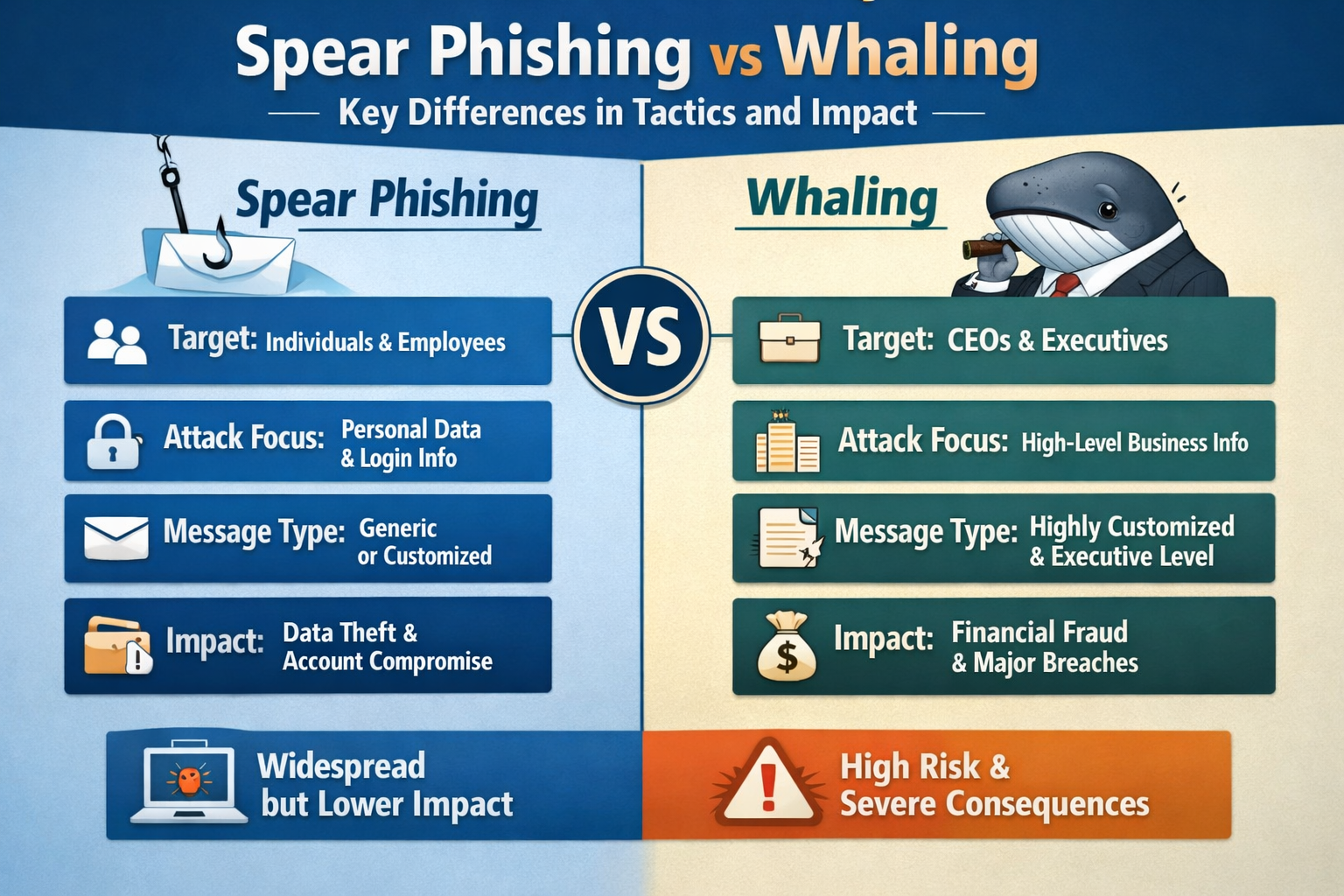
The clearest difference is who gets targeted. Spear phishing usually goes after a specific employee, department, or group with useful access. Whaling focuses on high-profile individuals with the power to approve transactions, expose sensitive data, or direct other employees to act.
So while a spear phishing attack may target an IT administrator or accounts payable staff member, a whaling attack is more likely to target a CEO, CFO, COO, CTO, General Counsel, or executive assistant working closely with leadership.
Both attack types use personalization, but whaling tends to involve more detailed profiling. Attackers may study an executive’s public statements, LinkedIn activity, communication style, reporting structure, business relationships, and current company events. Torq notes that attackers may mimic a senior leader’s writing style and use publicly available material such as press releases or professional profiles to make the message feel authentic.
Proton goes even further, explaining that attackers may examine social media, business websites, data brokers, and even the dark web to build a profile of what is most likely to trigger a response.
That is an important distinction. A regular spear phishing message might be personalized enough to fool an employee. A whaling message often needs to feel polished enough to fool someone who deals with sensitive decisions every day.
In many spear phishing campaigns, the attacker is looking for login credentials, access to corporate accounts, installation of malware, or a foothold into the network that can later be used for lateral movement. Imperva specifically notes outcomes such as stolen sensitive information, malicious program installation, and the opening stage of an APT.
With whaling, the goal is often more direct and higher stakes. Torq says these attacks commonly center on wire transfers, confidential M&A documents, and login credentials to critical systems. In other words, the attacker is often trying to trigger an immediate high-value action instead of simply gaining a starting point.
A spear phishing campaign may target several people across the same department or business unit. Huntress describes it as more likely to appear in broader coordinated campaigns. Whaling, by contrast, is often a single, highly customized operation built around one executive or one high-pressure business scenario.
That difference changes the tone of the message. Spear phishing often aims for access. Whaling often aims for authority and speed.
This is where a lot of articles stay too shallow. The issue is not just that whaling targets executives. It is that executives sit closer to money, strategy, legal documents, privileged systems, and high-trust internal workflows.
A fraudulent message sent to a junior employee can still do plenty of damage. But a fake request that reaches someone with the power to move funds, release confidential data, or approve a vendor payment can create catastrophic financial loss, compliance risk, and lasting reputational damage. Torq specifically frames whaling as having extremely high business impact because it can lead to direct losses and serious downstream consequences.
Huntress makes the same point through a real-world example. In early 2025, Arup’s Hong Kong office was hit by an AI-driven whaling scam involving deepfake video and voice clones, which convinced a finance employee to transfer HK$200 million, roughly US$25.6 million, to fraudsters.
Proton also references the 2015 Mattel case, where attackers used a highly targeted executive-themed request during a period of internal change. The fraud attempt involved a payment request tied to a realistic business scenario and nearly cost the company $3 million before the funds were recovered.
These cases show why whaling is often closely tied to CEO fraud, business email compromise, and other forms of executive impersonation. The attack is not always technically complex. It just needs to be convincing at the right moment.
Despite how polished these attacks can look, there are still patterns businesses should watch for.
A suspicious message may include:
- An unexpected request involving wire transfers, payment approval, tax forms, or confidential reports
- A sense of urgency that discourages verification
- A sender address or domain that is close to real, but not quite right
- A request to log in through a link rather than through the normal site
- Unusual timing, strange tone, or wording that does not quite match the sender
- A demand for passwords, bank account numbers, Social Security Number details, or other sensitive records
- A sudden request from a “senior leader” that bypasses normal approval steps
These attacks work because they feel plausible in context. A fake invoice, a payroll request, a file-sharing link, or a quick executive follow-up can easily blend into a busy workday.
No single control will stop every spear phishing or whaling attempt. The best protection is layered.
Security awareness training still matters because these attacks are built around human judgment. Huntress and Torq both stress the value of training employees and executives to recognize impersonation, pressure tactics, and suspicious requests. Executive-specific training matters because leadership faces a different style of attack than the average employee.
Multi-factor authentication and two-factor authentication also remain important. Imperva explains that even if a password is stolen, 2FA can prevent an attacker from using it without the second factor.
Email-level protections matter too. Torq highlights DMARC, SPF, and DKIM as important controls for reducing spoofing and helping verify legitimate senders. It also points to sandboxing, suspicious email analysis, and AI-powered phishing detection as useful parts of a modern defense.
On the process side, businesses need stronger verification workflows. Large payments, changes to banking details, payroll exports, and sensitive document requests should require out-of-band verification through a trusted channel. If an email says the request is urgent and cannot be verified, that alone should raise suspicion.
There is also a practical benefit to password managers. LastPass notes that password managers can reduce password reuse risk and help prevent users from entering credentials into fake websites, since autofill usually works only on the legitimate domain.
Finally, reporting needs to be simple. Employees should know exactly where to forward suspicious messages so the IT or security team can review them quickly. The faster a phishing email is reported, the better the chance of limiting the blast radius.
In most business settings, whaling tends to be more dangerous per incident because it targets people who can move money, expose strategic data, or trigger organization-wide consequences. But that does not make spear phishing a lesser threat. A successful spear phishing email aimed at the right employee can still open the door to malware, stolen admin credentials, broader account takeover, and a deeper compromise of the network.
The better way to think about it is this: spear phishing often gives attackers access, while whaling often gives them leverage.
That is why the comparison matters. They are closely related threats, but the difference in target audience, research depth, payload, and business impact changes how companies should prepare for them. If a business only trains staff to spot obvious scam emails, it is not ready. Modern attackers study people, mimic trusted behavior, and exploit the pressure points that exist inside real organizations.
A strong defense starts with one simple mindset: do not trust urgency just because it comes wrapped in familiarity.