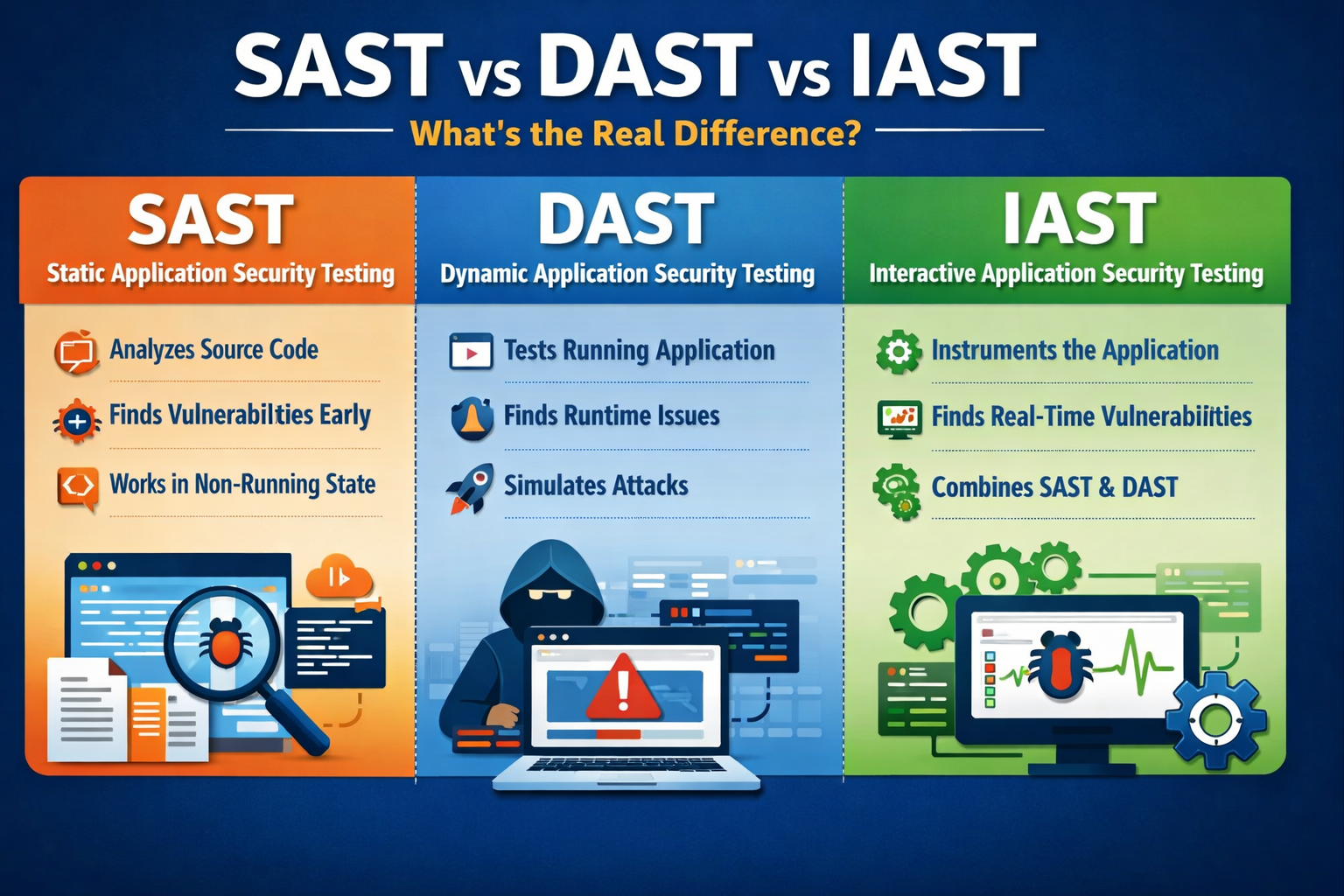
If your team is trying to tighten up application security, it is easy to get lost in the alphabet soup. SAST, DAST, and IAST all exist to help find security vulnerabilities, but they do not do the same job, and they do not belong at the same moment in the SDLC. The clearest way to think about them is this: SAST looks at code before the app runs, DAST tests a running app from the outside, and IAST analyzes the app from the inside while it runs. That is why strong AppSec programs usually treat them as complementary, not interchangeable.
SAST, short for Static Application Security Testing, is the code-first option. It inspects source code, bytecode, or binaries without running the application, which is why it is often described as white-box testing. Because it happens early in development, teams use it to catch insecure patterns, risky data flows, and mistakes like hardcoded secrets before the build moves further down the pipeline. It also fits naturally into pre-commit hooks, pull requests, and other early CI/CD checkpoints.
That early visibility is SAST’s biggest strength. Fixes are usually cheaper when found earlier, and developers can often pinpoint the exact file or line that needs attention. But that same early view also creates a tradeoff. Since SAST is not seeing the app in motion, it can be noisy and generate false positives, especially when runtime behavior, frameworks, libraries, or real request flows matter. In plain English, SAST is excellent at spotting potentially risky code, but it is not always the best at telling you whether that risk is truly exploitable in a live environment.
DAST, or Dynamic Application Security Testing, comes at the problem from the other side. Instead of reading code, it tests a running application like an attacker would, which is why it is usually described as black-box testing. Official OWASP guidance describes DAST as testing a running application by injecting malicious payloads to uncover weaknesses like SQL injection, cross-site scripting, authentication issues, and server configuration mistakes. That outside-in view makes it especially useful in testing, QA, staging, and other pre-release environments where teams want to validate real behavior, not just theoretical flaws.
This is where DAST shines. It can catch issues that only show up when the application is live, including misconfigurations, broken authentication flows, and exposed paths that code-only scanning may miss. It is also more language independent, which helps in mixed stacks or applications built with multiple technologies. The downside is timing and visibility. Because DAST comes later, fixes can be slower and more expensive, and because it works from the outside, it may tell you that a problem exists without showing the exact line of code behind it.
IAST, or Interactive Application Security Testing, sits in the middle. It tests the application while it is running, but unlike DAST, it works from within the application through instrumentation or an agent. OWASP describes IAST as a testing method that examines the app while it is being exercised by automated tests, human testers, or any real interaction with the software. In practice, that means IAST can see the actual code being executed, the control and data flow, the relevant HTTP requests and responses, and the surrounding runtime context.
That inside view is what makes IAST so appealing to many modern DevSecOps teams. Because it combines elements of static analysis and dynamic analysis, it tends to produce more precise findings, with fewer false positives and better line-level guidance for developers. It can also show which vulnerabilities are actually reachable and exploitable during real test activity. The tradeoff is that IAST needs a working application and meaningful test coverage. If a feature is never exercised in QA, integration tests, or staging, IAST will not see it.
When people ask about SAST vs DAST vs IAST, they are usually trying to find one winner. That is the wrong frame. The real difference is not which one is universally best. It is what each one can see, and when it sees it. SAST is strongest when code is still being written. DAST is strongest when you want to validate a running application from the outside. IAST is strongest when you want runtime insight plus code-level context during testing. Put simply, SAST sees code early, DAST sees exposed behavior from the boundary, and IAST sees what the application is actually doing from the inside.
That difference also shapes the kind of findings you get back. SAST is often the quickest way to catch insecure coding patterns before release. DAST is better for confirming exploitable issues in the real application surface, such as authentication gaps, misconfigurations, or injection flaws. IAST is especially helpful when teams want higher-confidence findings tied to actual execution paths, file locations, and stack-level context. So if your question is, “Which tool tells developers exactly what to fix?” IAST often has the edge. If your question is, “Which tool finds problems before the app even runs?” that is clearly SAST. If your question is, “Which tool sees what an attacker sees?” that is DAST.
For most engineering teams, SAST belongs early and often. It makes sense in the editor, at commit time, and in pull request workflows where developers want quick feedback before insecure code spreads further. DAST usually belongs later, when there is a deployed target to test in staging, QA, or another environment that mirrors production closely enough to reveal real attack paths. IAST fits best when teams already have a working test process and want deeper, more actionable feedback during automated testing or structured manual testing.
This is also why mature teams stop framing the decision as either-or. Snyk explicitly notes that no single testing methodology provides complete vulnerability coverage, and that relying on one method creates blind spots. That aligns with what other competitors are saying too. Imperva recommends using SAST and DAST together, while Bright frames the three methods as complementary lenses on the same security problem. In real-world AppSec, layering tends to work better than choosing one scanner and hoping it does everything.
If your goal is to catch mistakes early and keep developers from shipping obvious security flaws, start with SAST. If your goal is to validate how a real running application behaves from an attacker’s perspective, add DAST. If your team already has strong automated tests and wants higher-confidence findings with runtime context, IAST is often the most developer-friendly next step. The right answer depends less on hype and more on your team’s maturity, release process, and testing discipline.For many teams, the smartest setup is not SAST or DAST or IAST. It is SAST for early code checks, DAST for exposed runtime behavior, and IAST where deeper runtime insight will actually help developers move faster. That mix gives you earlier detection, better validation, and more useful remediation guidance without pretending one tool can do the entire job alone.