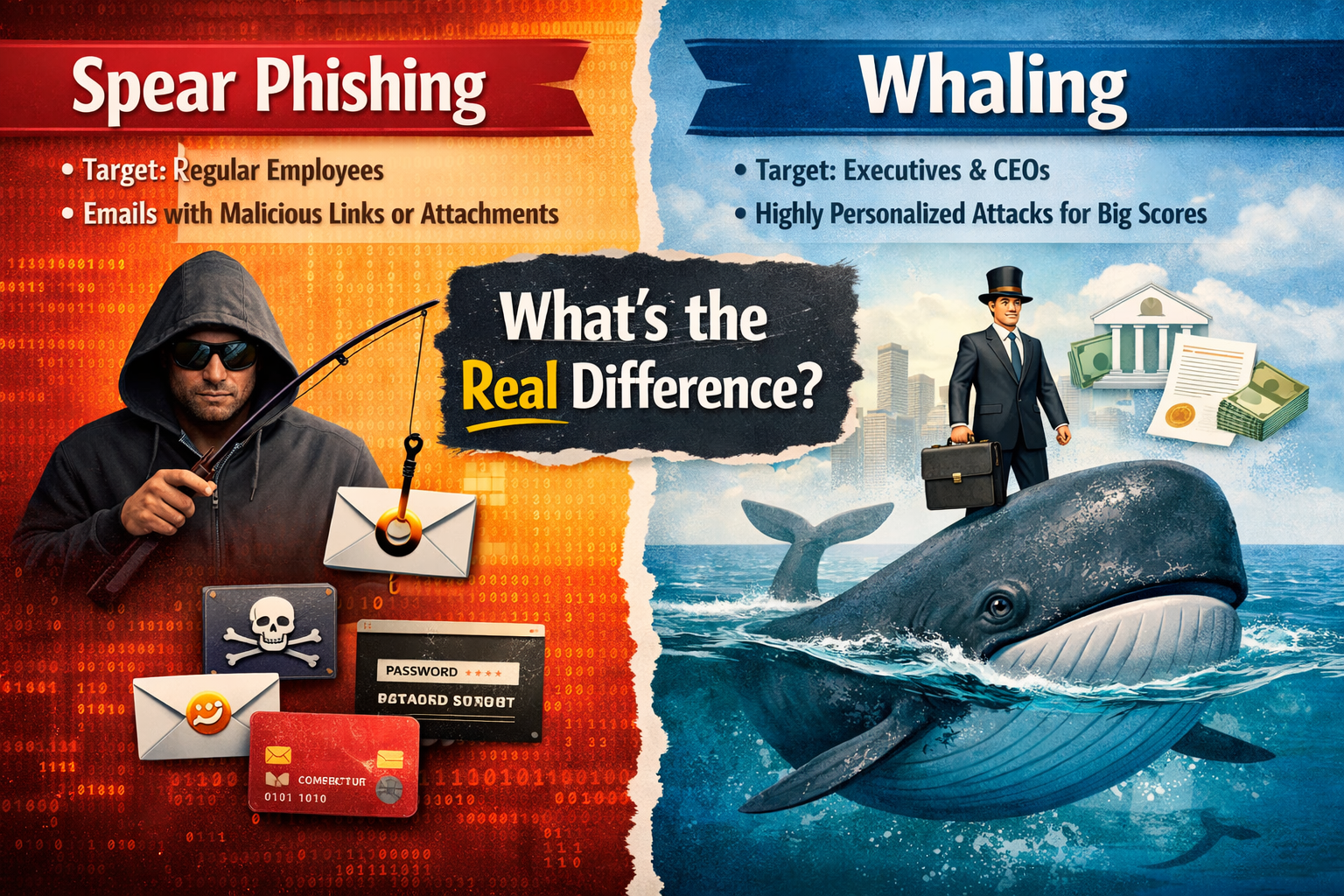
Most people hear spear phishing and whaling and assume they are basically the same scam with two different names. They are closely related, but there is an important difference that businesses should understand. Both are forms of phishing that rely on social engineering, trust, and carefully chosen details. The real split comes down to who is being targeted, how tailored the message is, and what kind of outcome the attacker is chasing.
If you run a business, manage a team, or simply want to understand modern email threats better, this distinction matters. A standard phishing email may go out to thousands of people at once. Spear phishing is more personal. Whaling is even more focused, usually going after senior leadership like a CEO, CFO, or other C-suite executives who have access to money, confidential records, and high-level decisions.
Spear phishing is a targeted cyberattack aimed at a specific person or group. Unlike generic mass-email scams, it is built to feel believable to the recipient. Attackers often research their target beforehand and use public information from social media, company websites, staff pages, or recent business activity to make the email feel legitimate. That message might mention a person’s role, department, coworker, or recent task so it seems familiar instead of suspicious.
The goal is usually to trick the victim into doing something useful for the attacker. That could mean clicking a malicious link, downloading a file, sharing login credentials, or handing over sensitive information. In many cases, attackers go after employees in HR, IT, finance, or accounts payable because those roles often have access to internal systems, payroll data, vendor payments, or other valuable business information.
Whaling is a more specialized form of spear phishing that focuses on high-value targets at the top of an organization. Think CEOs, CFOs, General Counsel, board-level leaders, and other senior decision-makers. These are the people attackers see as the biggest fish because they can authorize payments, access confidential reports, and influence major business actions.
A whaling email often looks polished and strategic. It may pretend to come from a trusted advisor, board member, legal counsel, or another executive. It may ask for approval on a large payment, access to a confidential document, or details tied to a legal or financial issue. Because the target is a senior executive, the tone is usually more refined, more businesslike, and more tailored to that person’s responsibilities.
The easiest way to explain it is this: whaling is a type of spear phishing, but not all spear phishing is whaling. Spear phishing targets a chosen individual or group inside an organization. Whaling targets top executives and other high-profile leaders.
That change in target also changes the stakes. A typical spear phishing campaign may be aimed at stealing credentials, dropping malware, or gaining access to a department’s data. A whaling attack is more likely to aim for a faster and larger payoff, such as a fraudulent wire transfer, a confidential financial report, strategic business information, or highly sensitive internal records.
Another difference is the level of personalization. Spear phishing is already highly targeted, but whaling usually involves even deeper research. The attacker may study the executive’s role, communication style, reporting relationships, and current business context to make the message feel credible. In other words, both are personalized, but whaling often pushes that personalization further because the reward is potentially much greater.
Whether the attack is spear phishing or whaling, the basic playbook is very similar. First comes reconnaissance. Attackers gather details from public sources, social media, company pages, and other online footprints. Then they craft an email that looks relevant and trustworthy. That message may impersonate IT, HR, a vendor, a colleague, or an executive. It may include a malicious attachment, a fake login page, or a request that sounds urgent enough to make the recipient act before thinking it through.
The pressure tactic is a big part of why these emails work. Attackers commonly lean on urgency, authority, and routine business language. They might frame the message as a payment issue, password reset, legal request, invoice review, or immediate approval. When a message looks familiar and urgent at the same time, people are more likely to respond quickly instead of slowing down to verify it.
Both threats are serious, but whaling usually feels more alarming because of the kind of damage it can cause in a single move. When a senior leader is tricked, the consequences can be much larger than a standard account compromise. One fraudulent approval can trigger a major transfer of funds, expose highly confidential information, or create significant reputational damage for the company.
That said, regular spear phishing should not be treated like a lesser problem. Many large security incidents begin with one employee opening one convincing message. Attackers do not always need the top person first. Sometimes they start with a staff member, collect access, and move deeper into the organization from there.
A lot of people expect dangerous emails to look sloppy, but that is often not the case with spear phishing or whaling. These attacks can be polished, specific, and well-timed. Still, there are some common red flags.
An email deserves extra scrutiny when it asks for credentials, payment approval, payroll data, or confidential files. The same goes for messages that pressure you to act immediately, click a link, open an attachment, or bypass the normal process. If the sender’s address looks slightly off, the request feels unusual, or the tone seems oddly urgent, that is a reason to stop and verify before doing anything.
For executives, the warning signs can be even subtler. A whaling message may sound formal and completely businesslike. It may reference a real board matter, vendor issue, lawsuit, or financial document. That is exactly why executive teams should not assume a polished email is a safe email.
The strongest defense is not just one tool. It is a combination of awareness, process, and security controls. Businesses should train employees to recognize social engineering, suspicious links, impersonation attempts, and unusual requests. Teams that handle payments, employee data, or internal systems need especially strong awareness because they are common targets in spear phishing campaigns.
It also helps to build verification into the workflow. If someone requests a transfer of funds, sensitive data, or a login reset, verify it through another channel before taking action. That simple habit can stop a surprising number of attacks. Technical protections matter too. Strong email security, multi-factor authentication, and a clear incident response process can reduce the damage if an attacker does get through.
For leadership teams, the bar should be higher. Since whaling is built around executive authority, senior staff need targeted training that reflects the threats they actually face. A generic awareness session is not enough when attackers are specifically designing emails for the people who can approve money, access confidential business records, or influence major company decisions.At the core, the difference between spear phishing and whaling is simple. Spear phishing goes after a specific person or team. Whaling goes after the biggest decision-makers in the company. Both are dangerous because both use trust, personalization, and timing to make a fake request look real. The better a business understands that difference, the better chance it has of spotting the threat before the damage is done.